by Jerry Stern
Webmaster, PC410.com
Westminster Maryland 21157
OK, the malware mess is gone. The popups are gone, your computer is running faster than it did when it was new. Background software has been chopped back so that only the software you really use is autoplaying at startup. Patches and plugins are up-to-date. And you have a new system backup or data backup. All that was included in your malware cleanup, if you had a professional do it. (Here in Westminster Maryland, that’s what is included in a malware cleanup if I do it. Elsewhere, ask questions if the job doesn’t seem complete.)
Right, what’s next? The computer is clean now. Is there more to do? Yes. There’s are more prevention steps to take.
- Ask: why was your computer infected? Usually, a computer tech can tell what infections are in a computer being cleaned. Not always–the newer items may not have names yet, but based on where on the computer the bad files were found, sometimes we can tell you that the malware arrived through an infected Excel file (Macros were enabled), or a PDF (Adobe Reader had Javascript on, Trust Manager on, or Acrobat was out of date), or a known Windows hole (Windows Update wasn’t running). So ask what the tech found, and close that hole–your surfing habits or the email lists you’re on will likely expose your computer to the same malware again, and it shouldn’t be able to get back in.
- Are you using a good security program? Your antivirus software, now usually called Endpoint Protection, didn’t stop something that it should have stopped. Ask your tech to look at what software you’re running for security. The best-known brand names are not remotely the best products.
- After a malware cleanup, always be suspicious. There’s a tendency to re-infect a computer, if you restore an infected backup, or go back to an infected web site, or your brilliant offspring re-installs their game cheat codes that were really a trojan horse password stealer. “Clean” means updated, patched, and not infected; it doesn’t mean impervious to harm, vaccinated, or safe.
- Check your backups. Create them if you haven’t already. The worst malware infections are easy (smaller cleanup invoice) if there is a good backup to work from. You should have image backups (keep the 3 most-recent ones), data backups (keep several months), and a permanent archive of old data, kept offline and updated on a schedule.
- Change your computer passwords and user account: Your computer password should not be blank. Also in Windows, if there are multiple user accounts for you and the kids, the most-common setup I’ve seen is that Dad has a limited account for surfing–that’s terrific, it prevents many infections, but Junior has an administrative-rights account so that he can download game cheats, and there’s no password there, so not only is his account at risk, but so is the rest of the computer, because the administrative-rights account can access nearly everything in the other accounts, in most setups, and can always reset every other password on the machine. Think: Who paid for that PC? All accounts which have administrative rights must have passwords. Limited or restricted accounts can have passwords for privacy, but don’t absolutely need them, because these accounts can’t install software.
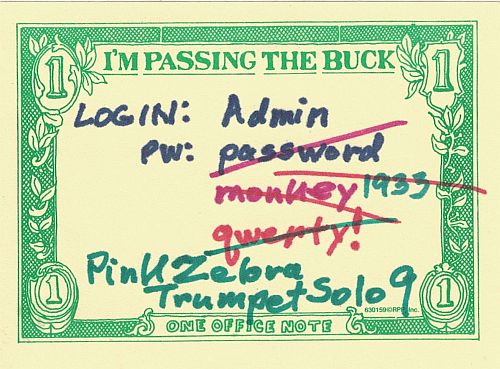
- Change your online passwords: Your computer was recently the property of a bot-farm. Or it had spyware on it, or malware that was doing just about anything it wanted to, because while it was infected, it didn’t belong to you. Any password on it was basically either removed or stolen. Change the important ones.Which passwords are important, and must be changed after a cleanup? Anything that connects to banking, credit card, and payment accounts, online profiles that include modifying web pages (like Facebook, LinkedIn, any web-editing logins like WordPress or Joomla), email accounts (to stop any bot that received your login credentials from sending mail with your login from some other system). Basically anything that’s being used to spread spam or malware–that’s all of the above. All right, there’s scary stuff out there on this topic. Let’s be sane now. A password of “password” is not security. Neither is the date your youngest child was born, or “123456”. Similarly, a password you can’t type in, like “3923(%$jrDSfadf0oo-dsaSD)FSdf” is suitable for military work, but on a webmail account? There has to be some moderation. Passwords should be different for each place they’re used, should not be guessable by anyone reading your Facebook profile, and should be somewhat complex. There should be no dictionary words, no names of family members. In general, combine two things that aren’t related to the password’s use, into a nonsense word/number/punctuation combination that you can type without messing it up.
- Audit your online stuff: There’s a market for stolen online credentials, and you really need to look at your online profiles and see if anything you can modify online has been changed. So check your online banking, credit cards, Paypal account, and so on, and see if there’s any new activity that isn’t yours. While you’re in there, change the password. If you’re a webmaster, check your pages–there are automated hacks taking over web forums and blogs, if they detect what looks like a login username and password. Check for new stuff, check for links on pages that you didn’t put there.
- Audit, scan, or replace your backups: Your cleanup tech might be able to tell you the infection date, but it’s not always reliable. Some malware waits a random number of minutes or weeks after infection before showing any popups or redirecting any search results. Kind of like incubating a disease… So assume that your recent backups are infected, and make new backups or scan the old ones. Which? Scan? Or replace? OK, if it’s a file-by-file copy of your data, scan it. If it’s compressed, like an “image backup” of the entire drive, replace it. Remember to send an extra backup set off-site, including a copy of the software that you would need to read it or restore it.
- Check the plugins: A plugin is software that runs in other software, to give it the ability to do more. These are also called Extensions or Add-Ins, and most web browsers use them, but most PC users do not, so a lot of spyware is hidden in plugins. All of them add security risks to your browser (more code, more holes), so if you’re not using a plugin, uninstall it.